The vendors within the emerging SD-WAN landscape come from different backgrounds and draw from diverse pedigrees. In order to position themselves early & favorably in this market, they logically advocate their respective legacy/strengths within the SD-WAN context. Some vendors can draw from multiple strong suites, and will focus on integrating their holistic Enterprise WAN value chain. All of them will try & plug any gaps in their offerings, to realize a complete SD-WAN solution.
I will start with a review of Silver Peak in this post, which alongside VeloCloud and Versa, is one of the SD-WAN solutions offered on the Dell EMC VEP family.
Silver Peak draws heavily from its roots in WAN optimization. It offers mature app classification and traffic treatment. Some other vendors who come from similar background include Riverbed, Aryaka etc. Its suite comprises of
- Edge Appliances (Silver Peak’s EdgeConnect), which will be the component now delivered as the Dell EMC VEP family unit,
- (Unity) Orchestrator for Centralized Policy, Control and Management, and
- (Unity) Boost – The key WAN Optimization Component which is where Silver Peak differentiate themselves from others. Note that (Unity) Boost is an optional component – the SD-WAN part could be delivered with or without Boost.
I will discuss Silver Peak both in the context of Dell EMC VEP, as well as a stand-alone solution.
Unity SD-WAN Solution
The Silver Peak Unity family comprises of the following components.
Unity Fabric
is the logical WAN Overlay/fabric, inter-connecting everything. Termed “Business Intent Overlay” or BIO, it implements overlays which are abstracted from the underlying transport. There is a device (VEP) at each end of connection, which produces an encrypted IPSEC tunnel from point A to B (It should be noted that Silver Peak only does encrypted tunnels, @256 bit). Cross-connect of carriers is possible, but recommended only for pure internet (i.e. two internet WAN connections).
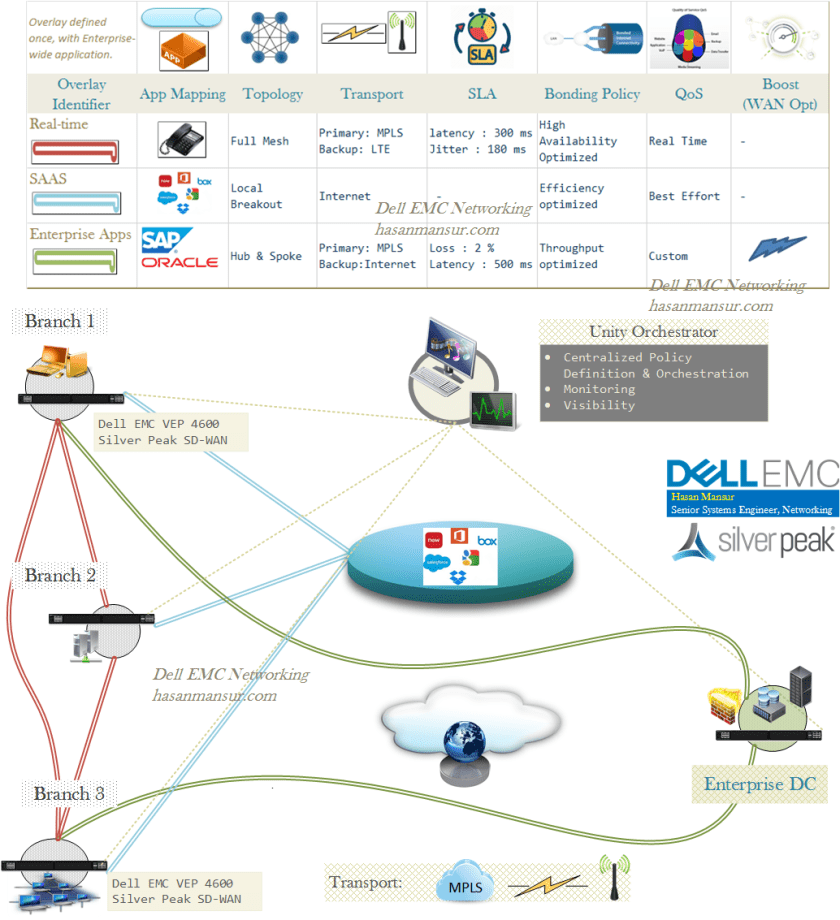
BIO only needs to be established once for the whole Enterprise. Each overlay is mapped to its policy, which is built using criteria such as Topology, the WAN path to take, SLA, Bonding policy, the use of Boost and QoS.
Thus, different Applications, depending on their requirements, can find residence in suitable Overlays. for e.g.
- VOIP could be mapped to a Real-time Overlay Bracket.
- It would need a Full Mesh topology since Hub & spoke would introduce latency to the calls.
- WAN Transport could treat MPLS as primary.
- The SLA would be aggressive around latency, jitter & loss.
- The bonding policy would focus on Availability instead of efficiency
- QoS would be Real time instead of Best effort.
- SaaS applications could be mapped to a SAAS/Cloud Overlay Bracket.
- It would use Local Breakout as topology – to eliminate backhaul to the DC & unnecessary bandwidth consumption.
- WAN Transport could use Internet/Broadband as primary.
- SLA will not need a particular focus on latency, jitter etc.
- Bonding Policy could focus on efficiency.
- QoS focus could be defined as Best Effort.
- Additionally, Service Insertion for Firewall/Inspection may be required.
Thus, the BIO is a classification bracket that determines the treatment of mapped applications. The granularity of BIO derives from its building blocks, which in turn enable fine grained and deterministic treatment of traffic. If the Enterprise uses SAP, it can place SAP in the Enterprise App Bracket, with its topology defined as Hub & Spoke (Haul to DC), and its own set of QoS, SLA, Bonding, preferred Transport, & optional application of WAN optimization.
In the same way, different applications can end up in their own respective Overlays, and treated according to the criteria defined for that overlay. Version 8 allowed up to 7 Overlays, a number due to increase with subsequent revisions. Do note that while a site can be a part of multiple overlays, a device/appliance can only map to one deployment profile (Deployment Profiles are templates that control a site’s configuration and its connectivity).
Fabric Components
Unity Fabric is made up of the following components.
VEP / Edge Appliance
The Edge appliance will manifest as a Dell EMC VEP family unit like the VEP 4600. With VEP, the Silver Peak solution will be provided as a VM image on top of middlewear – there is no direct-on-baremetal option.
Prior to being offered on VEP, Silver Peak used to offer “EdgeConnect” as both physical & virtual appliance. Virtual appliance defaulted to out-of-path Server mode. Physical defaulted to in-path Router mode. EdgeConnect appliance sizes were based on bandwidth and throughput, and ranged from 100Mb to 10Gb. Virtual Appliance throughput however, was limited to 1 Gbps. With regards to provisioning/ZTP, unlike a hardware appliance, the virtual appliance did not have a serial number. It therefore required license information to be entered manually upon first boot. This in turn enabled it to register with the cloud portal, and request a serial. EdgeConnect did allow deployment into Azure or AWS.
Unity Orchestrator (GMS, Central Management & Data Plane Orchestration)
The Orchestrator manages the Edge (VEP) devices across the network. It is used to define & centrally assign, business intent policies. Using templates, Orchestrator can assign policies, requiring limited to no manual intervention (This is one of the SD-WAN value prop – Agility via Automation and Centralized policy definition). It makes control decisions, and gives visibility of your network. All Edge devices and licensed capabilities are listed in the Orchestrator. It is Out of path of data, so if the instance is offline, it does not impact data.
Prior to integration with VEP, Silver Peak used to Offer the Orchestrator as an On-prem VM (Free of charge), Or as a service.
Unity Boost (WAN Optimization)
Boost is an optional performance pack that is an on-demand subscription. It’s for applications where acceleration matters. For example, data replication.
Unity Boost represents Silver Peak’s Core strength. This is where it draws from its roots in WAN optimization.
Boost is a combination of
- Data De-duplication,
- TCP Acceleration &
- Compression
It is consumed in a capacity model, which can be thought of as the SD-WAN fabric buying capacity (in 100 meg chunks), which can then be applied to any Edge device (branch location etc.) anywhere in the fabric – whenever & wherever needed. Thus you buy a capacity instead of a Wan optimization box, provision it only when you want, and remove it when it is no longer needed.
Cloud Portal
is another component in the Silver Peak solution – A license portal/db sitting in AWS, involved in zero touch provisioning. The cloud portal talks to both
- Orchestrator (polls portal once every minute), and
- Edge devices (licensed 30 days at a time & tries to update daily).
Typically, a new device would call home to the cloud portal & presents its serial number, to consume it’s provision. Devices would periodically re-register.
Unity SD-WAN Features
I have tried to summarize and group the feature set offered by Unity. we might look into these in more detail in part 2 of Silver Peak Overview. For now, here is the summary:
Path Conditioning
- Context: Reliability
- Components:
- FEC – Forward Error Correction (for Loss Mitigation): FEC enables rebuild of packets which are lost in transit. This is achieved by sending Parity data, alongside regular data. The device at the Remote end of the tunnel computes the content of lost packets, to eliminate re-transmission. Note that packet loss due to chronic congestion on the link, will not be alleviated by FEC, and could infact result in further degrade. Silver Peak solution is capable of dynamically adjusting FEC in response to link conditions, to minimize overhead.
- Link Bonding (Not load balancing): Link bonding can be thought of as FEC executed over multiple links. The payload and the parity packets are spread over multiple transports (e.g. MPLS and Broadband). Link Bonding & FEC, is tandem, can potentially start achieving the performance of private lines.
- Modes: Link Bonding modes offer a number on options, and can be optimized for Resiliency or Throughput
- High Availability: 1:1 FEC. Can only use 2 active paths at a time. The trade-off for HA is bandwidth consumption, as packet duplication reaches 1:1 ratio.
- High Throughput: This is Round Robin load balance between active paths, enabling aggregate bandwidth use. Variable Auto-FEC ratio of 1:5.
- High Quality: Prefers Best Path. Variable Auto-FEC ratio of 1:5.
- High Efficiency: Most efficient use of Aggregate bandwidth, but the trade-off is lack of protection from FEC/loss.
- Packet based multi-pathing is a feature of Link bonding, alongside
- Brownout awareness.
- Modes: Link Bonding modes offer a number on options, and can be optimized for Resiliency or Throughput
- POC – Packet Order Correction : is the Silver Peak Edge device correcting the order upon reception of packets, prior to delivering them to the internal network. Out-of-Order packets are inherent to packet switched networks.
- QoS Shaping (Prioritize critical Apps/Traffic): up to 10 unique traffic classes or QoS profiles may be defined. the Shaping applies only during congestion.
- Ingress shaping ensures business critical apps do not suffer due to lower priority apps.
- Egress shaping assures WAN bandwidth is not monopolized by any single app.
The Solution can dynamically switch paths during blacks outs or when brownout thresholds exceeded.
Dynamic Path Control
- Context: Traffic Steering – Application Aware Routing & High Availability
- Components:
- Traffic Steering based on
- Application (for e.g. Real-time Apps sent over MPLS, others over internet)
- Link Quality (choose Least-Loss, Latency or Jitter)
- Load Balance (for High throughput/availability) based on
- Percent utilization of the Tunnel Bandwidth.
- Per-Packet – Packets distributed proportionally across aggregated link, then re-assembled on egress.
- Sub-second failover
- Traffic Steering based on
Boost
- Context: WAN Optimization
- Components:
- Network Acceleration – TCP Proxy + Acceleration : This makes use of techniques such as adjustable window sizing, transporting more payload within a single delivery window etc. There are certain requisites to Acceleration:
- Edge devices on either end, see full TCP handshake.
- Symmetric Flows. (If flows are asymmetric, they can’t be accelerated, but can be treated with NM (below) & FEC + POC)
- Network Memory: De-Duplication & Compression : This is about reducing Congestion via Data Reduction.
- De-duplication is Byte Level, executed by utilizing Byte Fingerprints
- It cannot work on encrypted traffic
- Network Acceleration – TCP Proxy + Acceleration : This makes use of techniques such as adjustable window sizing, transporting more payload within a single delivery window etc. There are certain requisites to Acceleration:
SaaS/IAAS Optimization
- Context: SaaS Optimization
- Silver Peak calculates closest Egress point from customer’s WAN to each SaaS Service.
Application Focused Security
- Context: Security, App Classification, Traffic Steer, SAAS breakout
- First Packet IQ: Silver Peak can identify apps/domains on the first packet. Consequently, this enables
- Granular App steer
- Intelligent SAAS breakout
- While the competition also offers identical feature, First Packet IQ is a key Silver Peak strength. With ability to detect 10,000+ Apps, it is way ahead of the competition (e.g. Viptela ~3000, Riverbed ~1300).
- Service chaining
- Web gateways (Zscaler)
- Next-generation firewalls (Palo Alto, Fortinet, Check Point)
We will carry on the review of Silver Peak SD-WAN solution in the next post. As noted above, some of the key strengths of the Silver Peak solution are around WAN optimization & First Packet IQ (App classification). The next post will focus more on Silver Peak SD-WAN deployment modes/models.
